As quantum ‘Q-Day’ leaps forward to 2029, Ethereum faces a new battle over what to do with coins left in old wallets.
The cryptocurrency industry has framed quantum computing as a single catastrophic “Q-Day” moment when sufficiently powerful machines arrive, old encryption keys are broken, and blockchain history is unraveled. This week, that moment may have been brought forward this decade.
The Ethereum Foundation’s March 24 Post-Quantum (PQ) Roadmap shows that realistic quantum threats to Ethereum are centered on forged signatures that enable theft and impersonation, and that choosing stronger cryptographic algorithms is a relatively manageable layer of the problem.
The coordination infrastructure underneath is much more difficult.
EF’s FAQ ranks the exposed surfaces in a specific order: user accounts (externally owned accounts, or EOAs), exchanges’ high-value operational keys, bridges, custody hot wallets, governance and upgrade multi-signatures, and validator keys.
Each category has a different migration schedule and political weight. Together, they describe a real-world financial system that must upgrade itself while running at full capacity, with hundreds of millions of accounts and no acceptable due dates.
Account abstraction is the default execution layer migration path for EF as it allows users to replace ECDSA-based authentication without forcing a chain-wide reset.
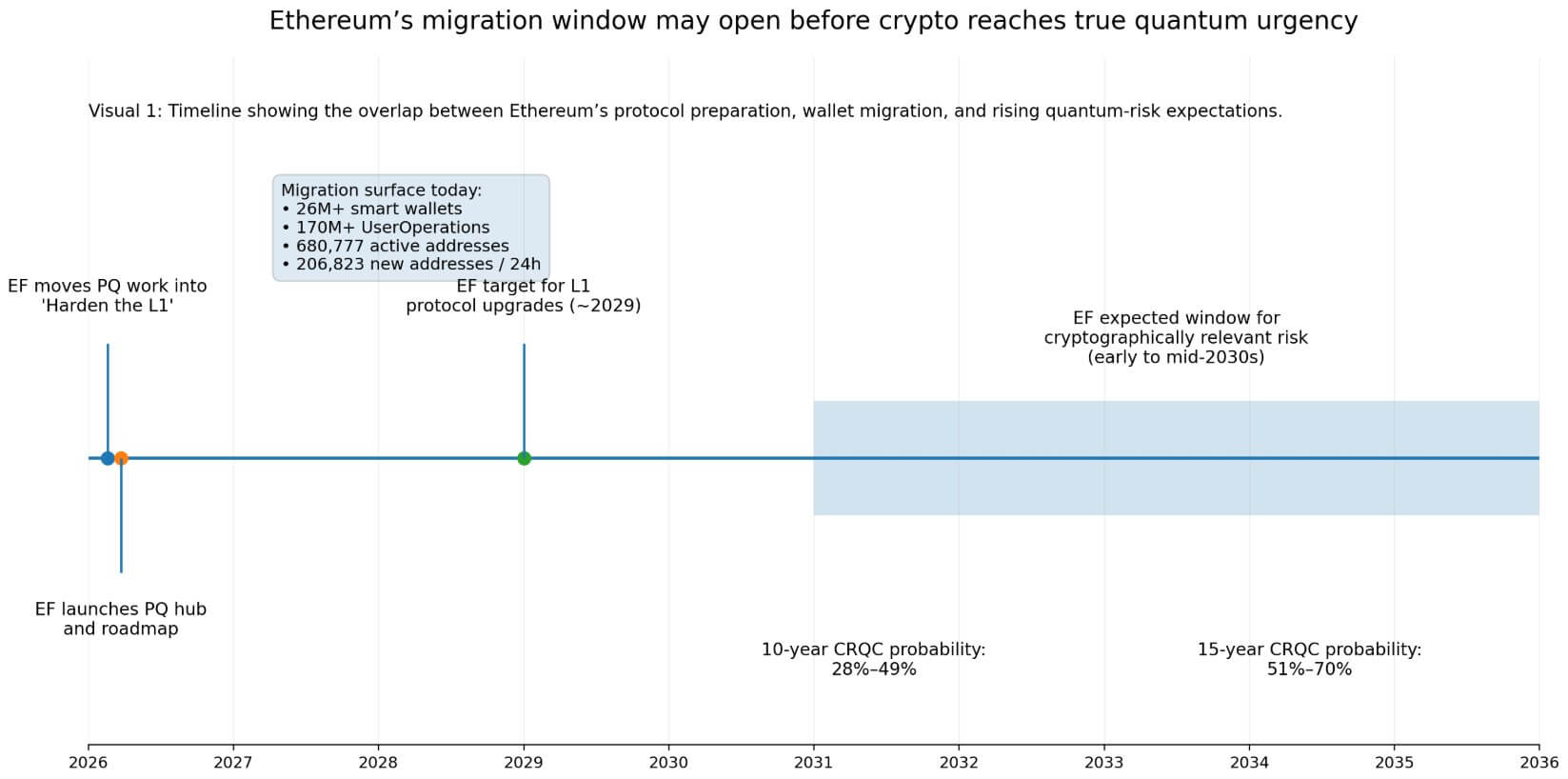
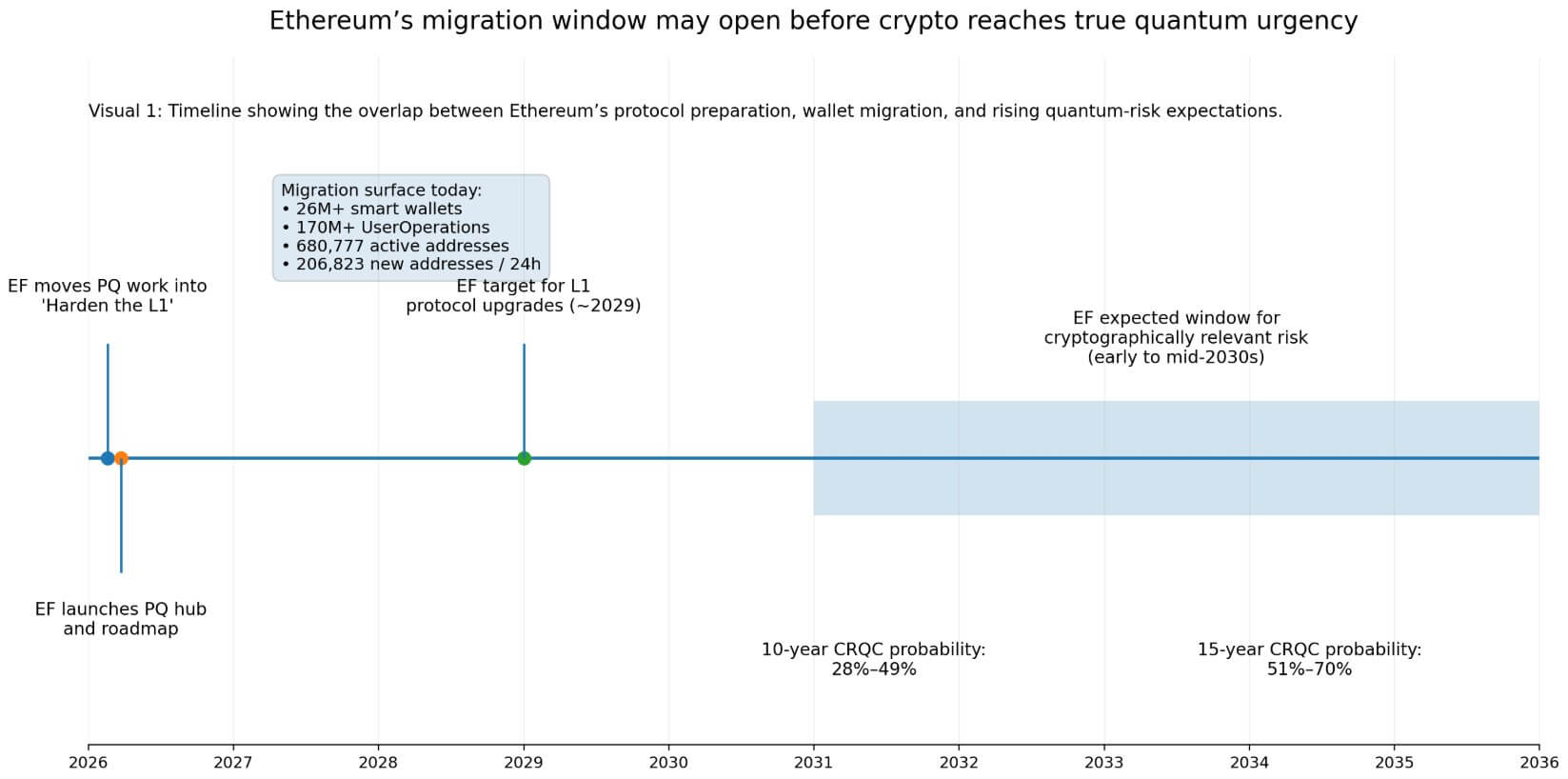
The EIP-4337 infrastructure already supports over 26 million smart wallets and 170 million UserOperations, which is still only a fraction of Ethereum’s active user surface.
DefiLlama currently shows around 680,777 active Ethereum addresses, with 206,823 new addresses in the last 24 hours.
According to the foundation’s schedule, the L1 protocol upgrade is scheduled for approximately 2029, with the full execution layer migration several years after that. EF says most expert roadmaps point to crypto relevance in the early to mid-2030s.
The Global Risk Institute’s 2025 Quantum Threats Survey puts the probability of cryptography-related quantum computers appearing at 28% to 49% within 10 years and 51% to 70% within 15 years, with respondents noting accelerated timelines.
The overlap between L1 preparation and user wallet migration is where operational exposure really arises.
But this week, that schedule looks even tighter. Google’s new warning compresses policy and market timetables even though the science remains uncertain. Google is now planning for Q-Day 2029. There is no set date when cryptography-related quantum computers will arrive, but it will change the frame of their operation.
As major infrastructure operators begin budgeting and planning for shorter timescales, post-quantum readiness will no longer be a distant research topic, but a near-cycle execution problem for wallets, bridges, custodians, and validators.
Where capital and control are concentrated
The bridge and archival layers make the exposure quite sharp.
L2Beat shows L2 connected to Ethereum locking up about $32.54 billion in value, DefiLlama shows Ethereum’s bridge protocol locking up a total value of about $7.275 billion, and Bridgerail has handled about $18.835 billion in volume over the past month.
These flows are executed through a relatively compact set of key management choke points. These are exactly the “high-value operational keys” that EF places second in their risk hierarchy.
Infrastructure attacks on keys, wallets and access control systems will account for the majority of cryptocurrency hacking losses in 2025, reaching $2.87 billion, outpacing smart contract exploitation, according to TRM Labs’ January 2026 Crime Report.
The operational discipline required by the post-quantum roadmap in this area mirrors the discipline the industry is already failing at today, making bridge and custody key rotation urgent in both timelines simultaneously.
The validator layer adds another dimension to the coordination problem.
Beaconcha.in has approximately 976,204 active validators and 36.67 million ETH staked, which at first glance looks like a maximally distributed key migration problem.
At the corporate level, Lido holds 21.24% of net staking, followed by Binance with 8.73%, Ether.fi with 6.05% and Coinbase with 4.64%, with these four operators together controlling about 40.66%.
Validator key rotation is both a mass coordination problem and a concentrated operator problem.
| surface | Key Statistics | Why is it important? | risk type | Migration Issues |
|---|---|---|---|---|
| User Account/EOA | 680,777 active addresses; 206,823 new items / 24 hours | largest live surface | Theft/impersonation | User-specific migration |
| smart wallet rail | Over 26 million smart wallets; Operates over 170 million users | Existing migration path | Uneven adoption | UX + Wallet Tooling |
| bridge | TVL $7.275 billion; Monthly trading volume: $18.835 billion | Value is concentrated in a small core set. | Operational key corruption | Rapid institutional circulation is needed. |
| Ethereum connection L2 | Secured value of $32.54 billion | Large capital stacks depend on infrastructure. | Indirect ecosystem leakage | Coordination between systems |
| validator | Active 976,204; 36.67 million ETH staked | Huge set of validators | Network Operational Risk | Bulk + Intensive Operator Migration |
| Top Staking Entities | Lido 21.24%, Binance 8.73%, Ether.fi 6.05%, Coinbase 4.64% | Top 4 controlled companies combined 40.66% | operator focus | The initial mover sets the pace. |
As major staking platforms circulate keys early, migration momentum naturally builds, and smaller groups of validators clearly follow suit. When large operators drag their feet, the burden of compliance falls disproportionately on independent validators who lack the operational infrastructure to handle it alone.
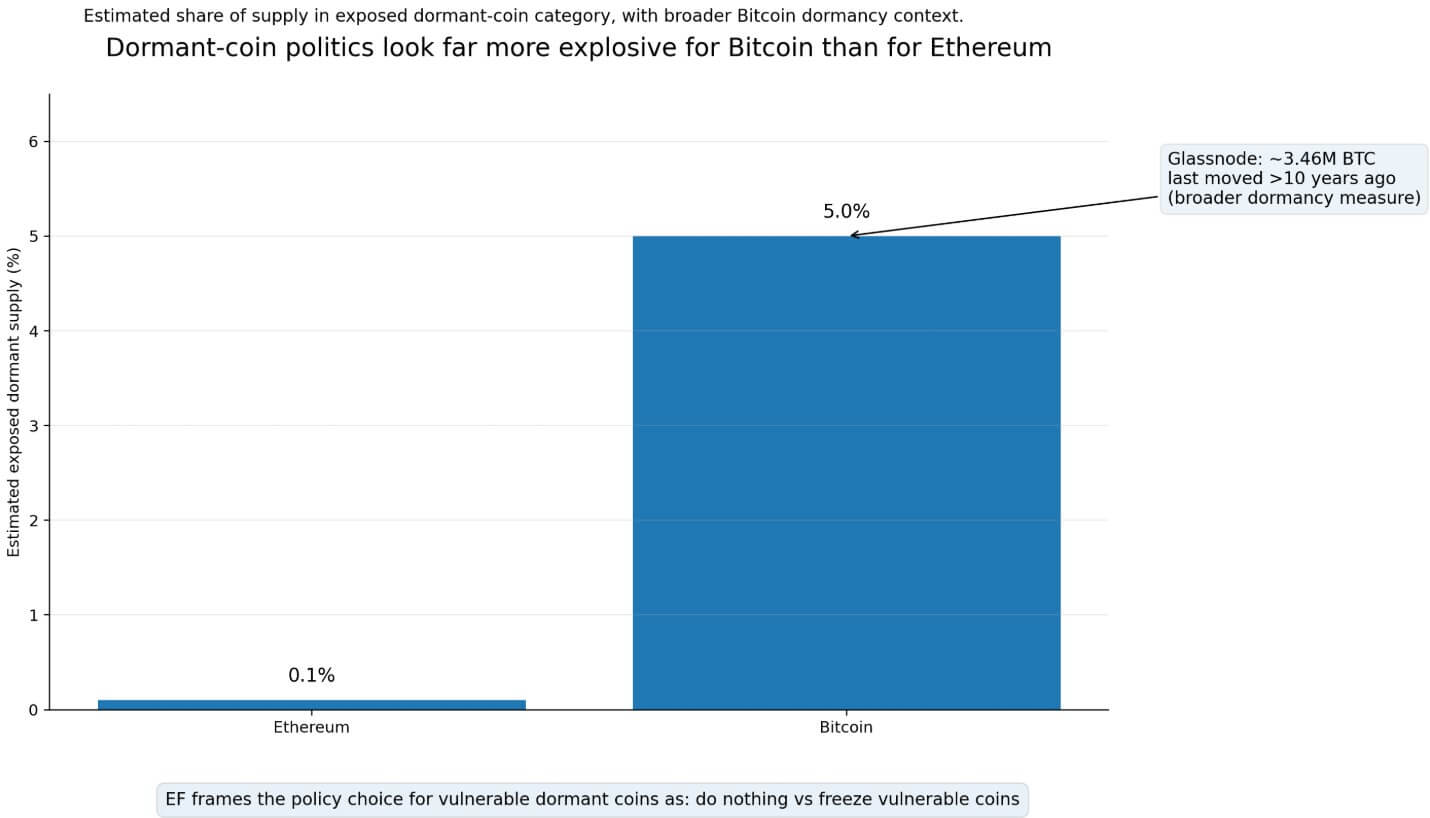
EF frames the dormant coin case as the most politically important element of its roadmap.
Accounts that have never revealed their public keys have no direct quantum exposure because the keys are hidden within their addresses.
Accounts that transact, expose their public keys and then remain silent are a completely different category and do not have their own migration mechanism, leaving your funds vulnerable.
EF’s FAQ lists two natural consequences that occur when a risk period arrives: Either do nothing or freeze vulnerable coins. EF explicitly frames that choice as a community governance decision. This requires social agreement on who is protected and under what conditions.
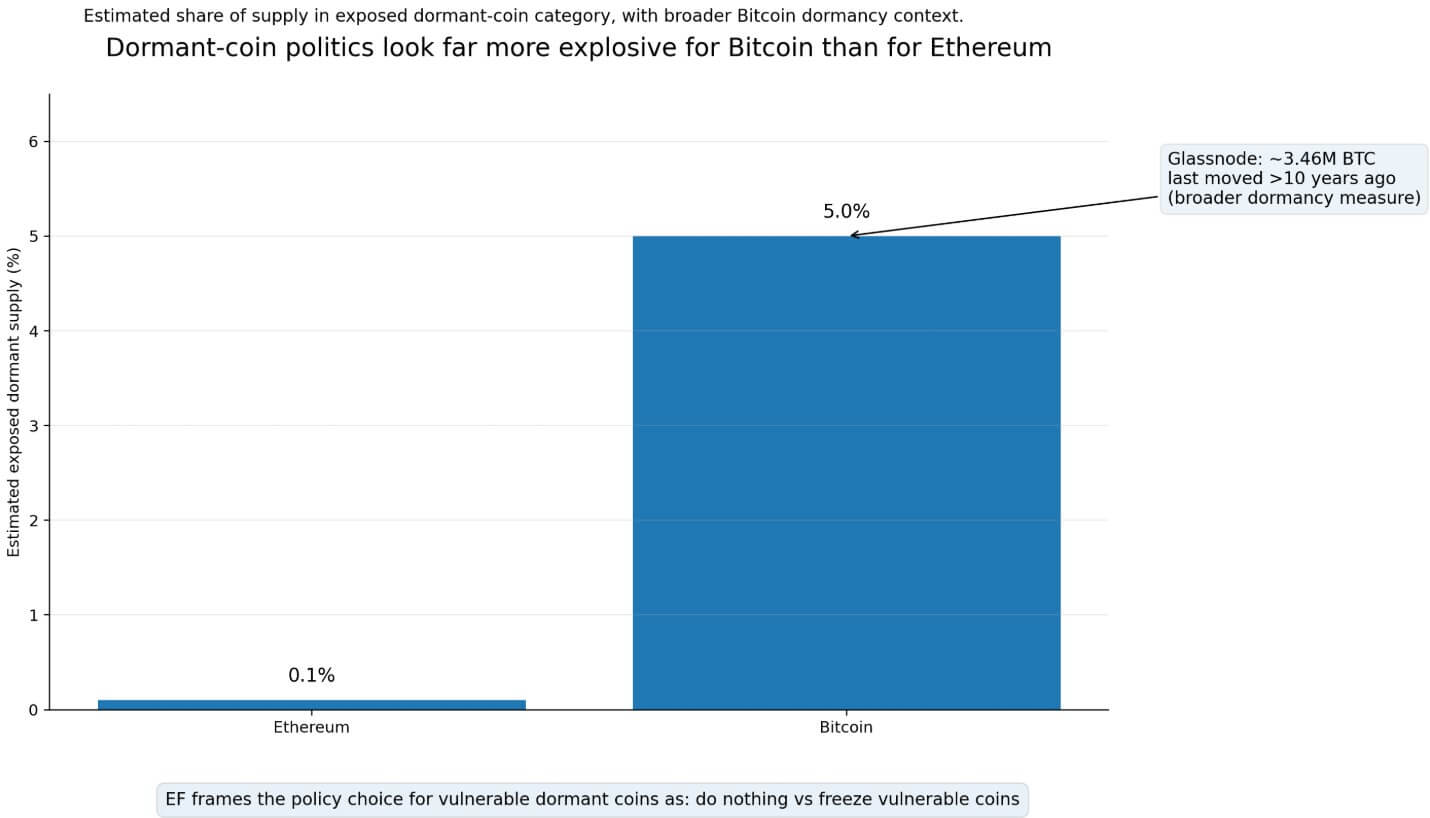
EF estimates Ethereum’s exposure in this category to be around 0.1% of supply, while Bitcoin’s exposure is closer to 5%, which is tied to the initial address format that many consider abandoned.
Justin Thaler of a16z argued that Bitcoin is uniquely exposed because the initial P2PK output places public keys directly on the chain, and because of Bitcoin’s governance structure, freeze adjustments are politically significant.
Glassnode shows that approximately 3.46 million BTC has been inactive for over 10 years. This is a broader measure of dormancy, which explains why arguments about dormant coins can happen much more easily in Bitcoin than in Ethereum.
two results
Ethereum is built on an account abstraction infrastructure that is already running at scale.
If the EIP-7702 and EIP-4337 tools allow a large number of active users to migrate before quantum instability reaches a retail tipping point, Ethereum may be able to absorb the transition without a governance crisis.
Bridges and custodians who control concentrated value and face institutional due diligence demands move first and establish migration standards across the industry.
Ethereum’s low dormancy exposure figures make “doing nothing” politically feasible and avoiding debate over chain freezes.
The real advantage of Ethereum in this scenario is its upgrade agility. That is, a live financial system that achieves quantum readiness through gradual, incentive-compatible migrations and preserves continuity and user experience throughout.
However, as the L1 milestone is delayed, execution layer migration extends deeper into the 2030s and quantum timelines shorten, the highest value surface is partially anchored to legacy assumptions. Especially if Google’s 2029 forecast comes true.
With infrastructure attacks already accounting for the majority of hacking losses today, markets are starting to price operational delays into security discounts for custodians and bridge operators before quantum computers are involved.
Post-quantum preparation will become a standard due diligence criterion for institutional allocators, and operators who cannot demonstrate a credible migration timeline will face capital outflow and increased insurance costs.
Crypto threats cause reputational and capital costs to accumulate during the migration period, driven by market perceptions of operational delays well in advance of crypto events.
EF placed PQ operations on the “L1 Enhanced” protocol track in February and explicitly linked the underlying accounting abstraction to quantum readiness. Encryption progresses according to a predictable schedule.
The migration battle over wallets, bridges, and dormant coins is already underway.



